
# Stupid Simple Network Inventory
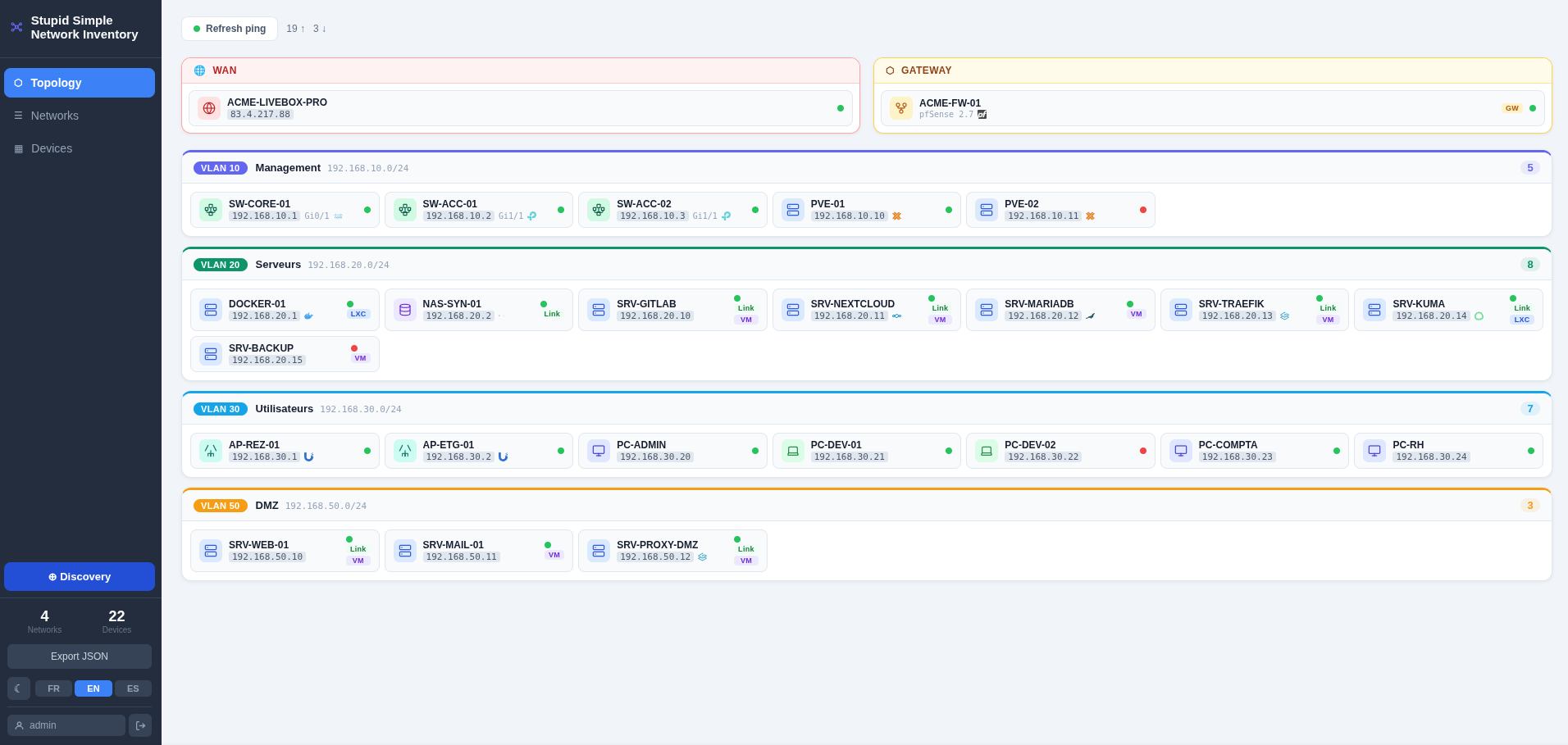
**Self-hosted network inventory and logical topology visualisation**
[Français](README.fr.md) · [Español](README.es.md)






[](LICENSE)
---
---
## ✨ Features
- 🗂️ **Manual inventory** — add and manage devices (21 types) with IPs, VLANs, descriptions and optional web links
- 🗺️ **Topology view** — card-based layout per network (LAN / VLAN 802.1Q), with WAN and gateway sections
- 📡 **ICMP ping sweep** — check reachability of all known hosts in one click
- 🔍 **Auto-discovery** — ping sweep + PTR DNS lookup on a subnet to import new hosts
- 🏷️ **Brand logos** — automatic detection and display of vendor logos (Proxmox, Cisco, Synology, Docker, 30+ more)
- 🔐 **Authentication** — JWT-based login with forced password change on first use
- 🌙 **Dark mode** — light / dark theme toggle
- 🌍 **i18n** — French, English, Spanish
## 🛠️ Stack
| Layer | Technology |
|-------|-----------|
| Backend | FastAPI + SQLAlchemy + SQLite (Python 3.11) |
| Frontend | Vue 3 + Vite, served by Nginx |
| Auth | JWT HS256, 24-hour expiry |
| Runtime | Docker Compose |
---
## 🚀 Quick start
```bash
# 1. Clone and enter the project
git clone https://git.raspot.in/olivier/stupid-simple-network-inventory.git
cd stupid-simple-network-inventory
# 2. Create the data directory owned by the current user
mkdir -p db_data
# 3. Configure environment (required for correct bind-mount ownership)
cp .env.example .env
# Edit .env:
# DOCKER_UID / DOCKER_GID → output of: id -u && id -g
# INITIAL_ADMIN_PASSWORD → set to avoid the default admin/admin bootstrap
# 4. Build and start
docker compose --env-file .env up --build -d
# 5. Open http://localhost:8080 in your browser
```
### First login
| Case | Credentials | Behaviour |
|------|------------|-----------|
| `INITIAL_ADMIN_PASSWORD` set | `admin` / `